Security Infographics
Visual guides to understanding cryptocurrency security, offline encryption, and protecting your digital wealth. Each infographic breaks down complex security concepts into easy-to-understand visuals.
New & Featured NEW
Fresh content on critical security topics
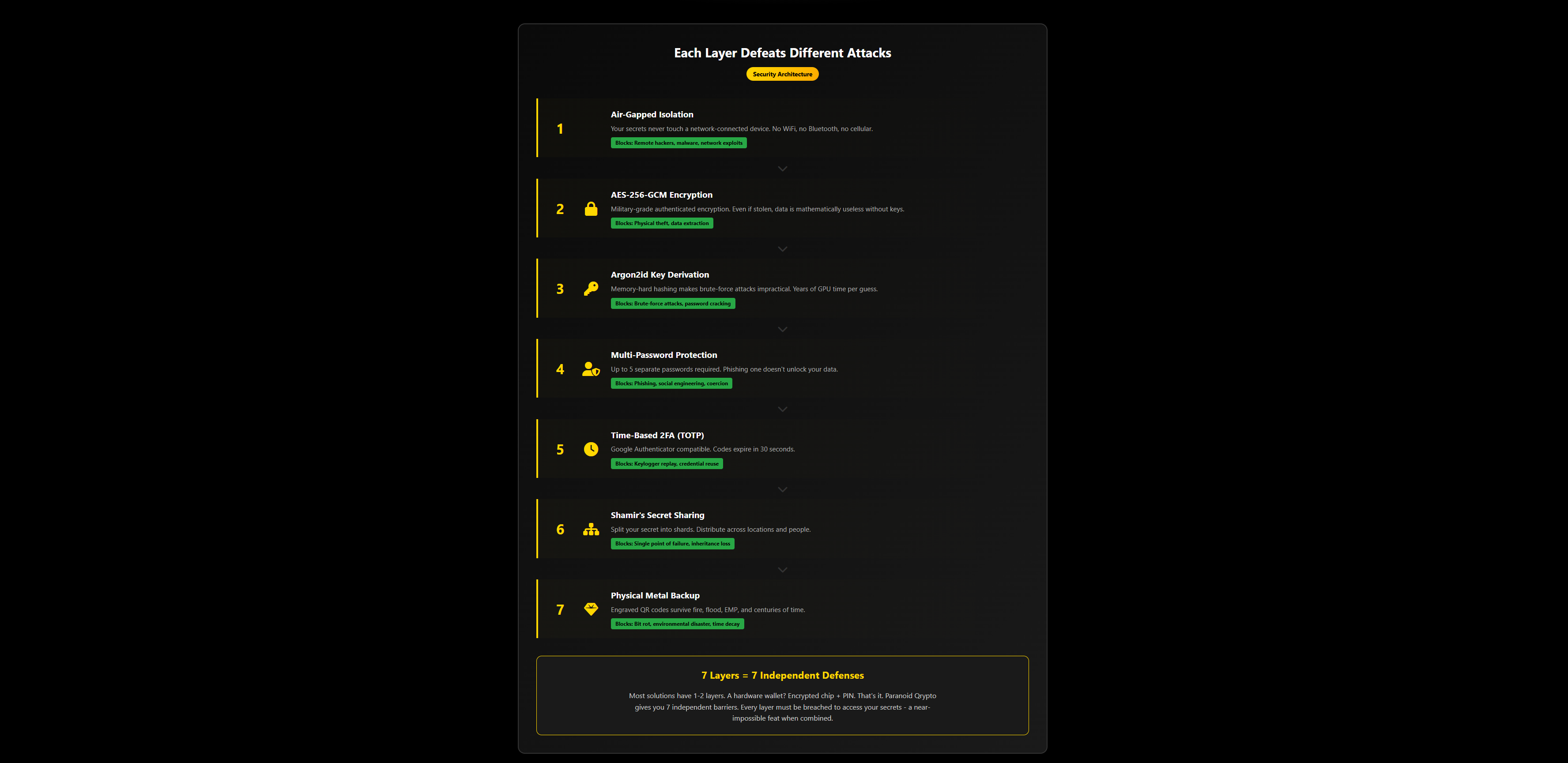
The 7-Layer Security Stack
Defense in depth: 7 independent security layers protecting your crypto. If one fails, others still defend.
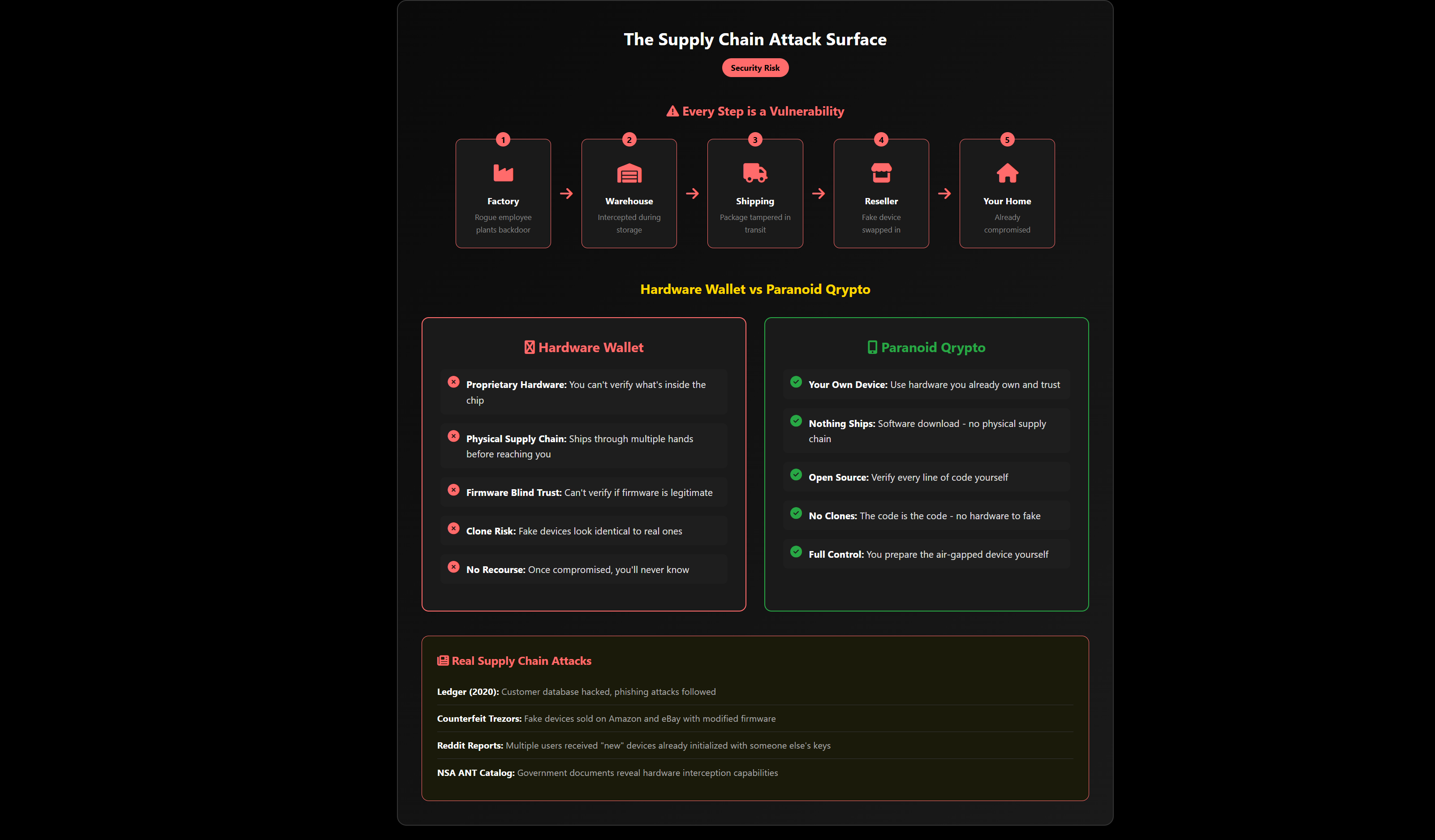
Supply Chain Attack Risk
Your hardware wallet's journey from factory to you - every step is a potential compromise point.
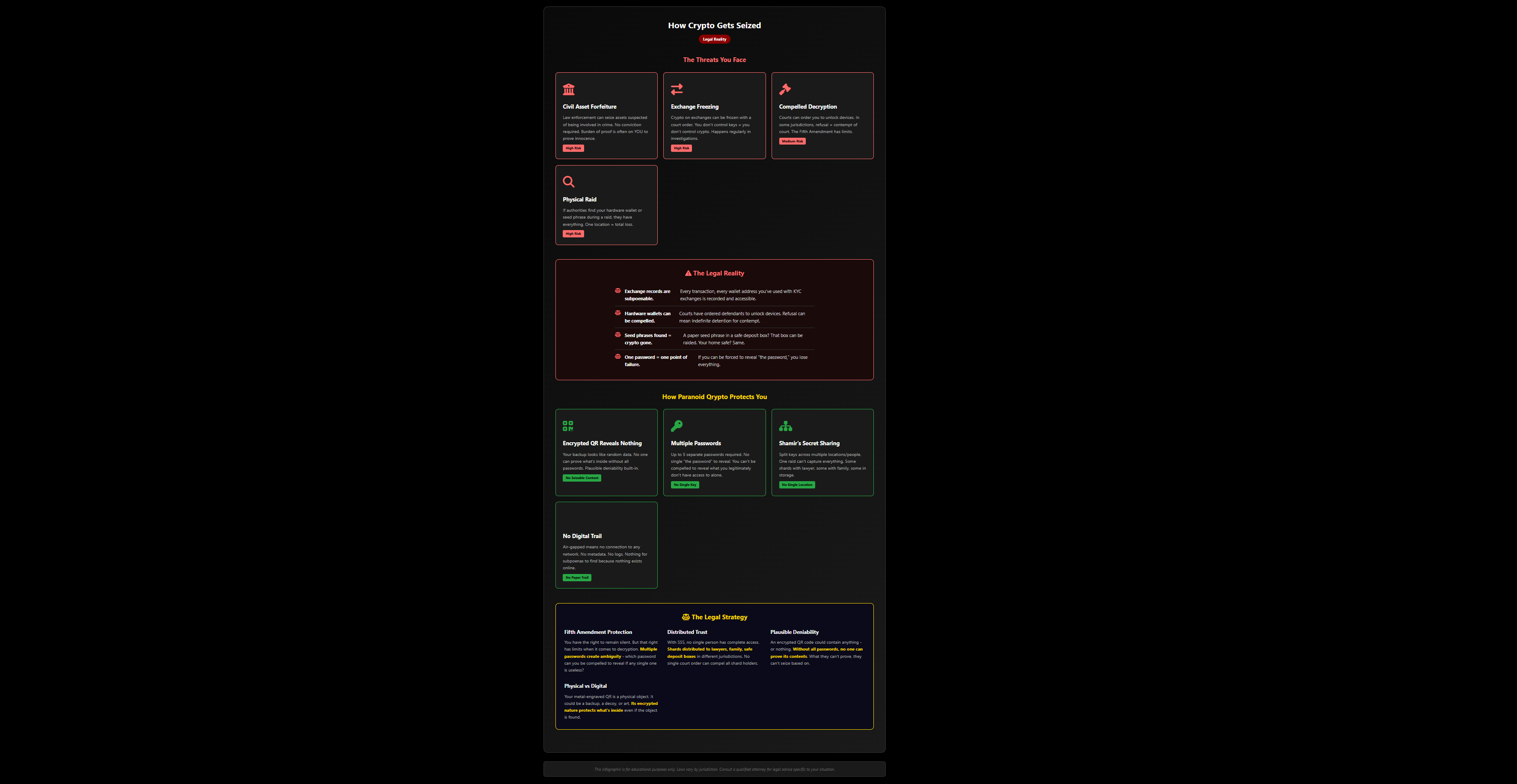
Government Seizure Protection
Civil asset forfeiture, compelled decryption, and how PQ's multi-layer approach protects you legally.
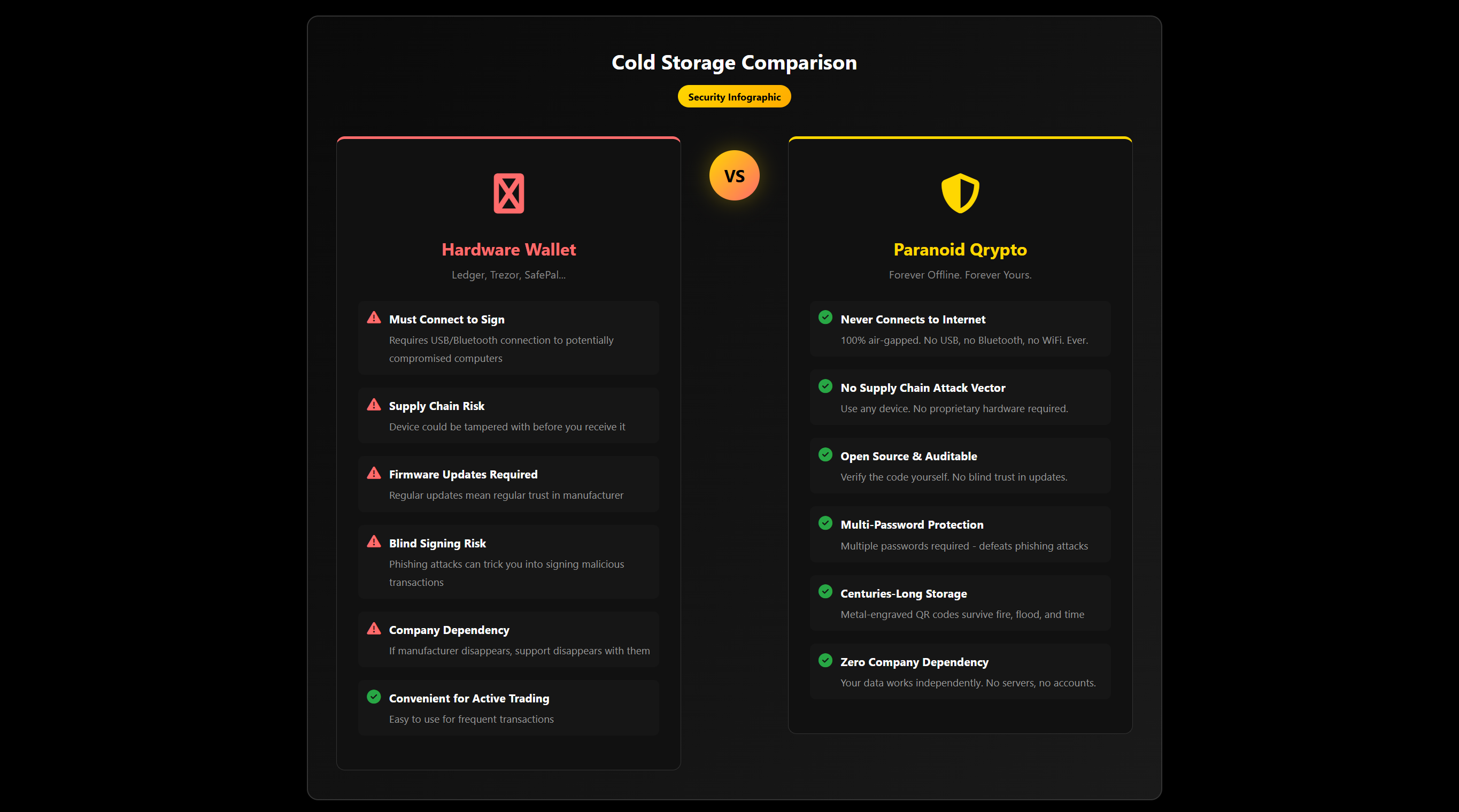
Hardware Wallet vs Paranoid Qrypto
The cold storage showdown. Compare Ledger, Trezor with air-gapped security.
Core Security Concepts
Essential knowledge for crypto security
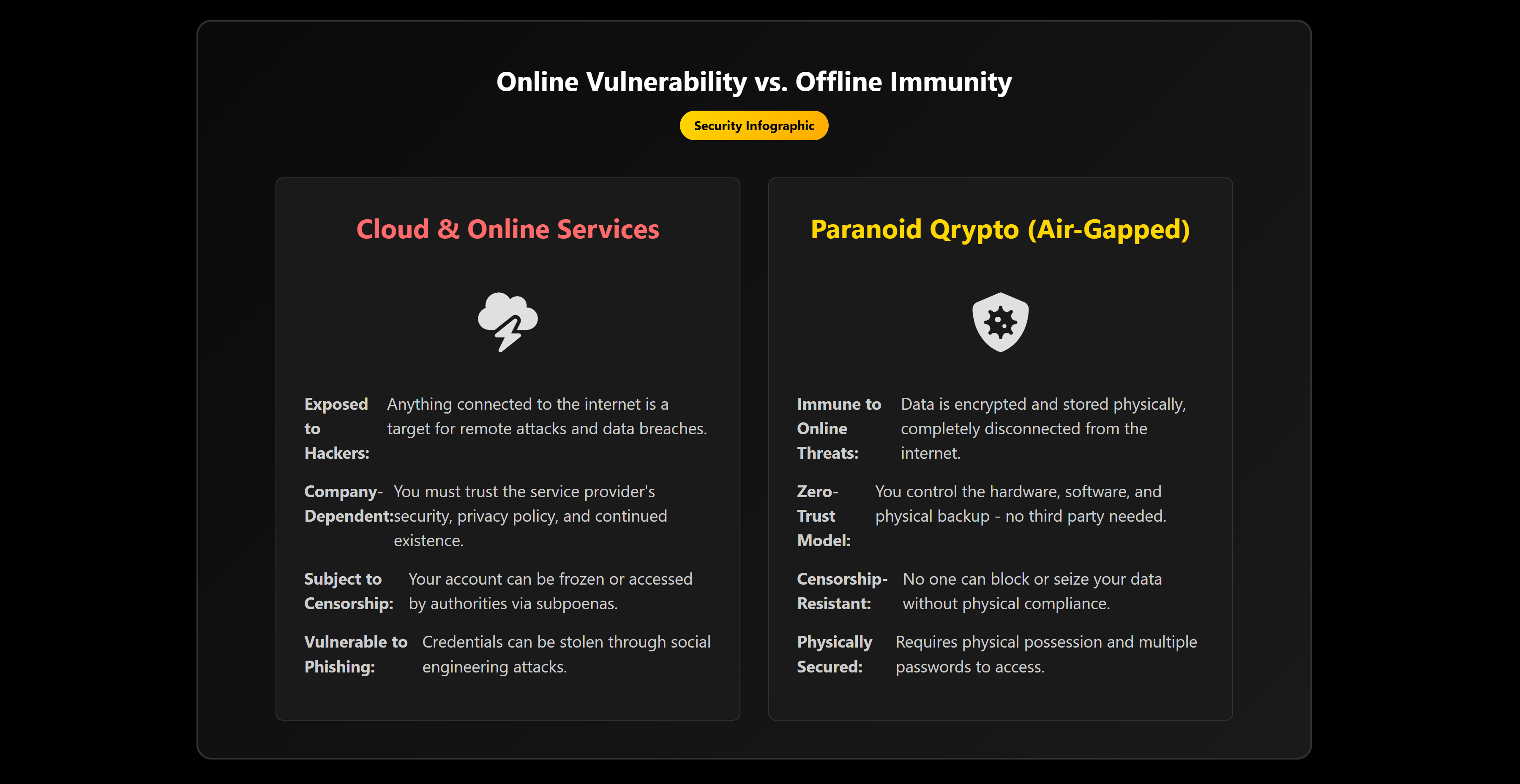
The Air-Gapped Advantage
Why offline beats cloud storage for security. If it's not connected, it can't be hacked.
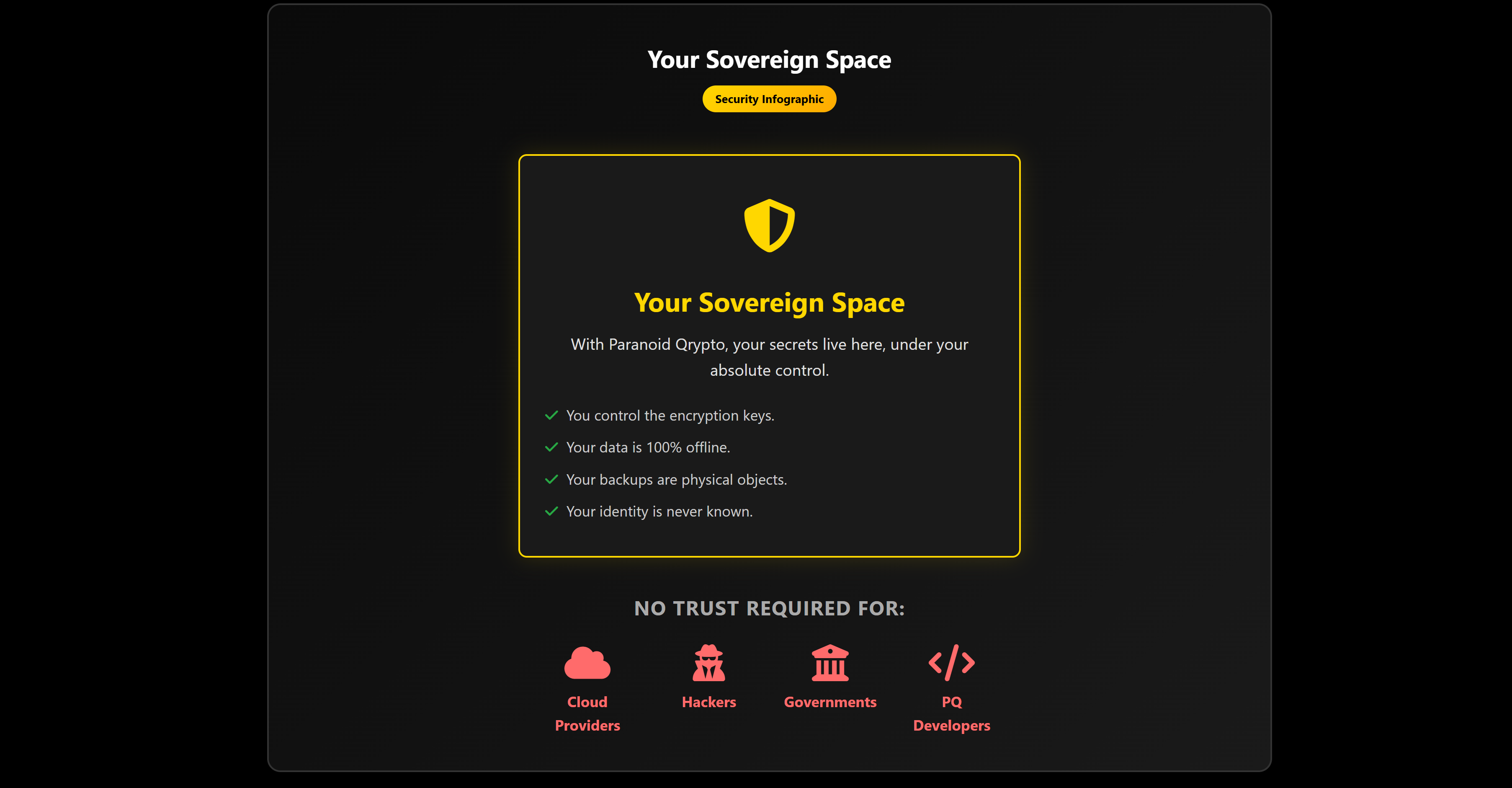
Zero-Trust Security Model
Never trust, always verify. Build a system where trust isn't required - not even in us.
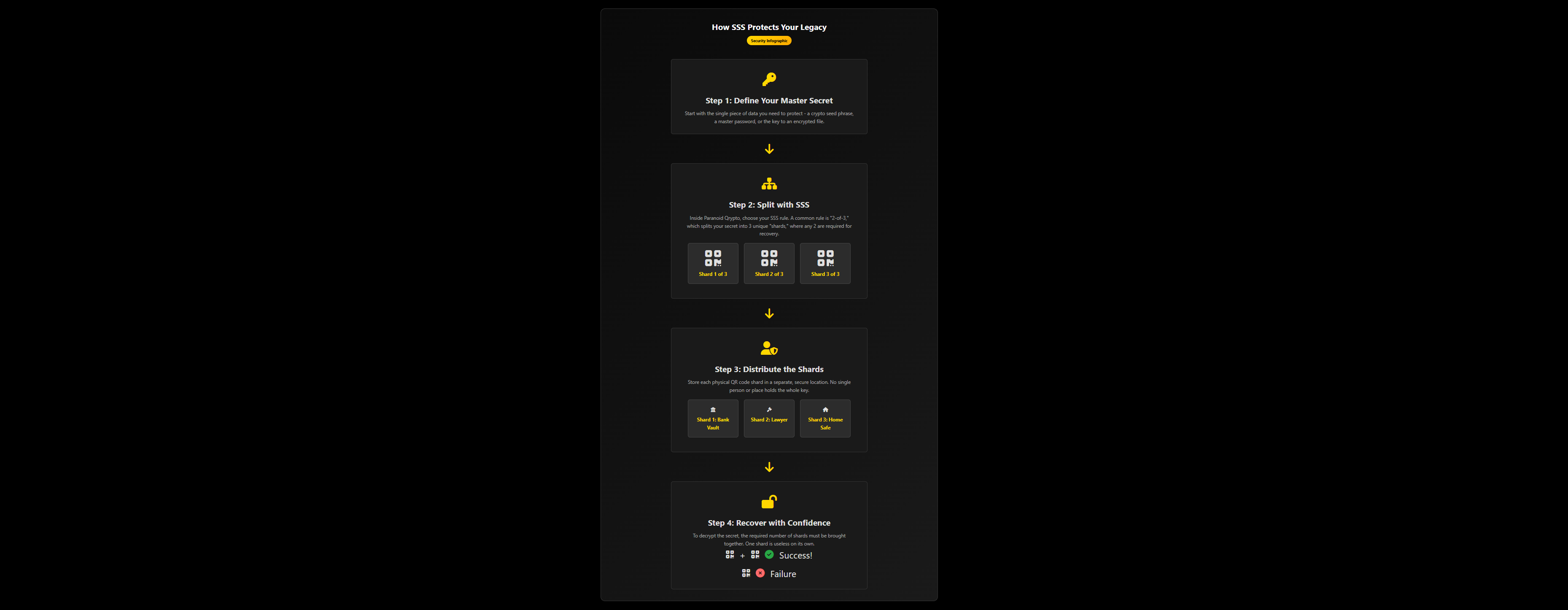
Shamir's Secret Sharing
Secure crypto inheritance planning. Split your secrets into multiple shards - no single point of failure.
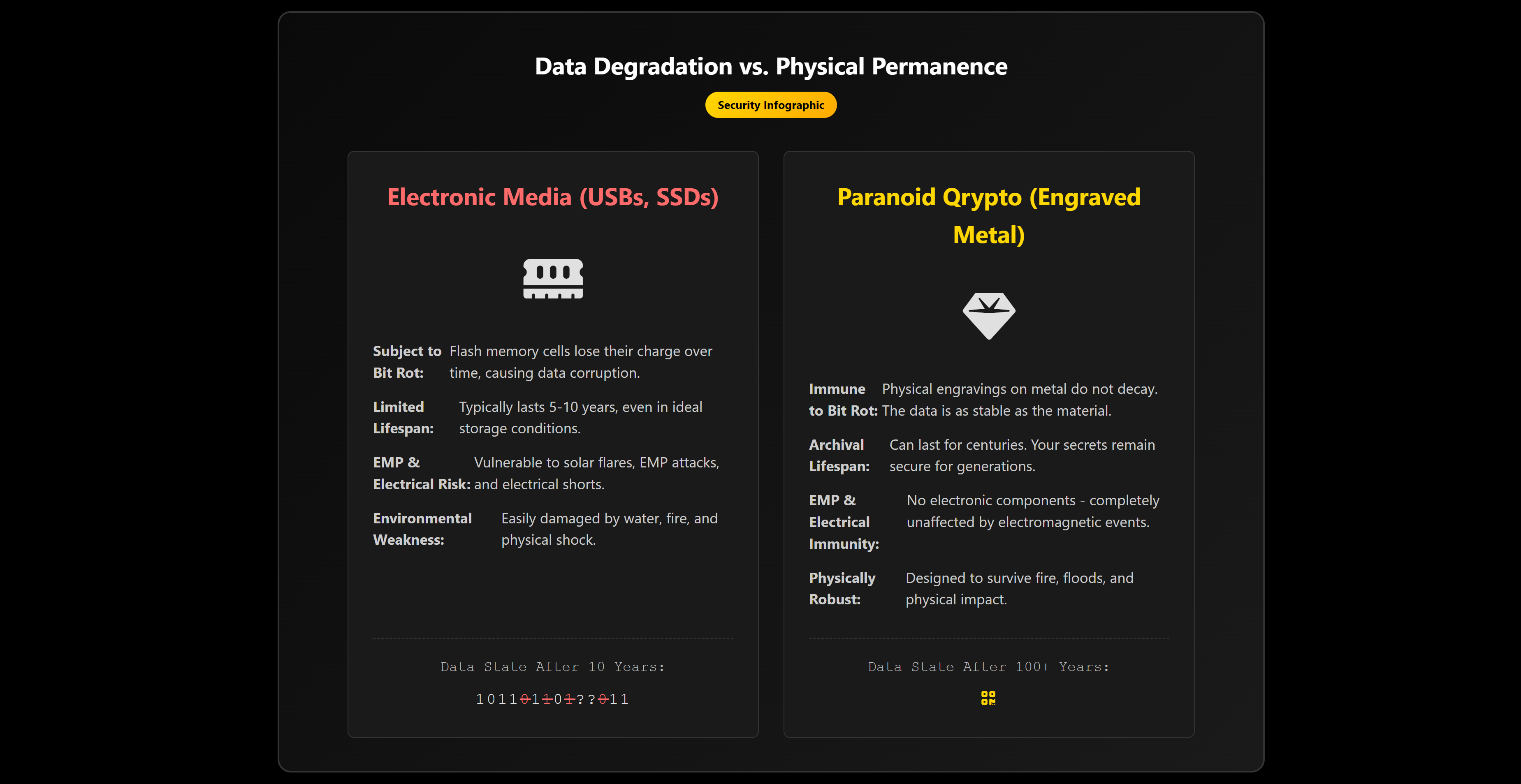
Bit Rot: The Silent Threat
Your USB drives and SSDs are slowly destroying your data. Why metal backups are the only permanent solution.
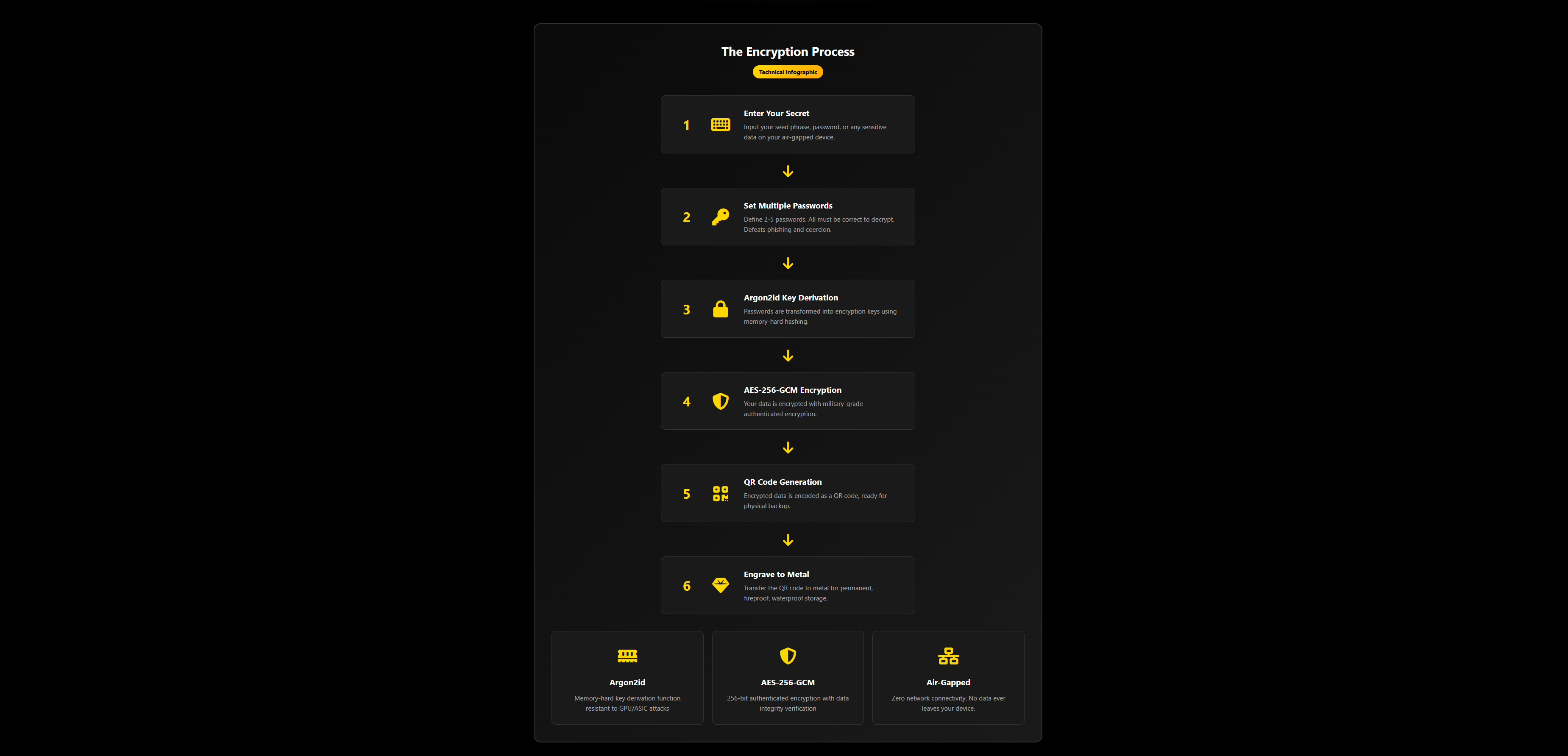
How Paranoid Qrypto Works
Step-by-step encryption process: from plaintext to engraved QR code using Argon2id and AES-256-GCM.
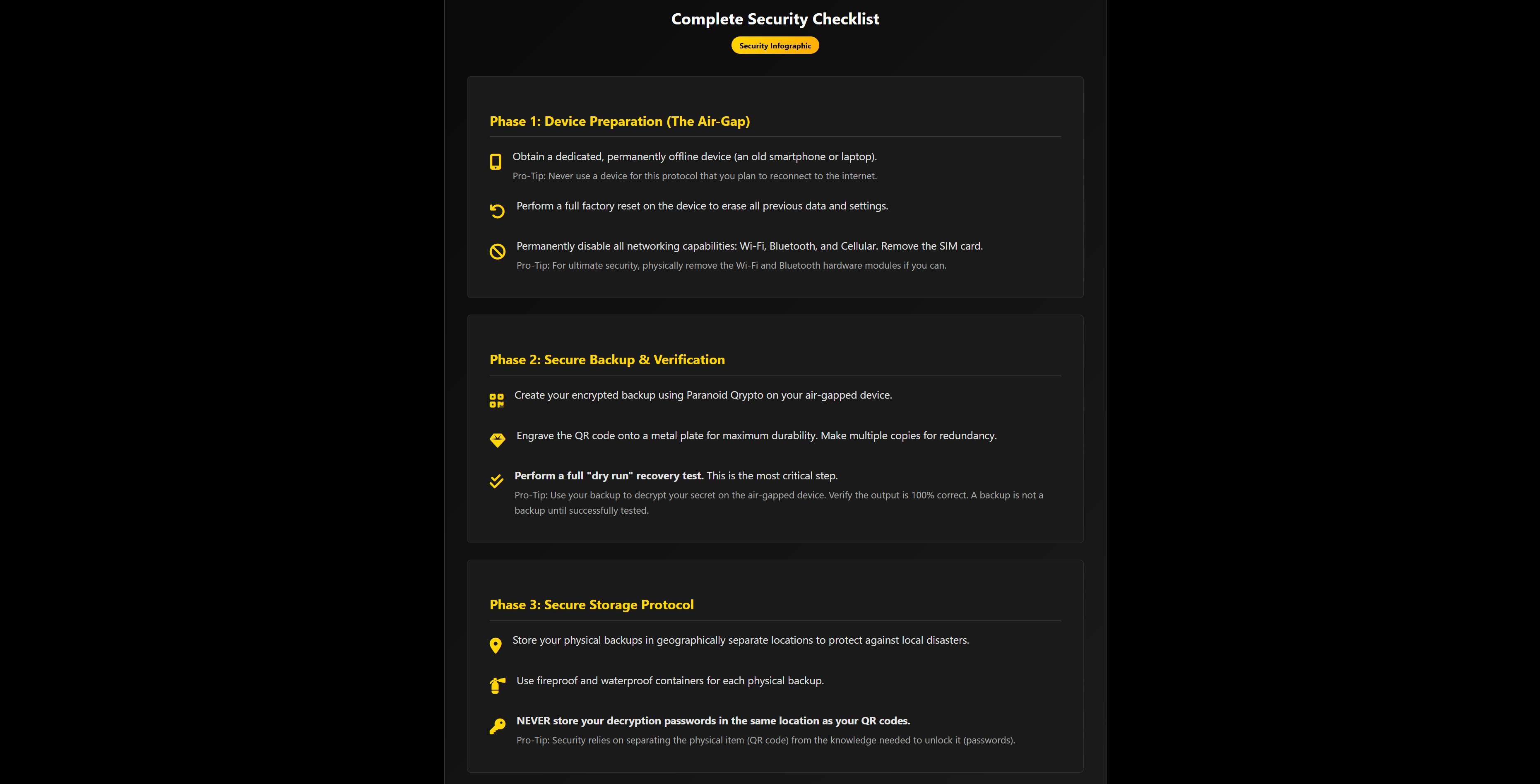
Security Protocol Checklist
Complete step-by-step guide: device preparation, secure backup, verification, and storage protocol.
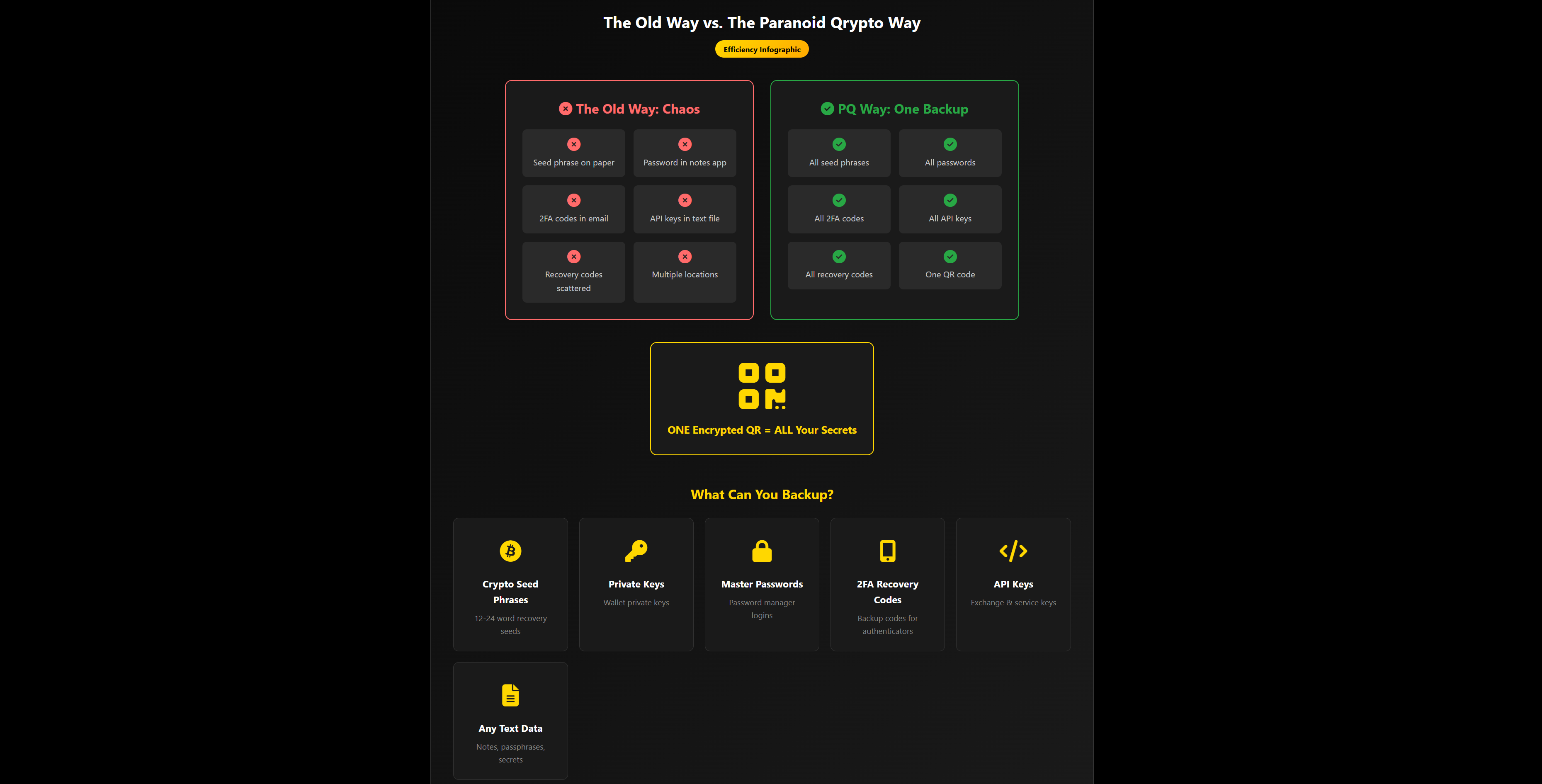
One Backup To Rule Them All
Stop juggling multiple backups. One encrypted QR code secures all your seed phrases, passwords, and keys.
Ready to Secure Your Crypto?
Download Paranoid Qrypto and start protecting your digital assets with military-grade offline encryption.
Get Paranoid Qrypto